Online Activity Documentation About Diehdfpem and Alerts Logs
Online activity documentation regarding Diehdfpem and alerts logs plays a critical role in maintaining digital security. It provides insights into user behavior and helps stakeholders manage potential threats effectively. Proper documentation enhances transparency and fosters trust among users. Additionally, it allows for optimized data management and resource allocation. However, the implications of inadequate logging can be profound. What strategies can be employed to ensure robust documentation and alert management?
Importance of Documenting Online Activities
Documenting online activities is crucial for various stakeholders in the digital landscape.
The importance of transparency emerges as a key factor, enabling organizations to build trust with users. By tracking user interactions, stakeholders can gain insights into behavior patterns, enhancing user experience.
This meticulous documentation fosters accountability and empowers individuals, ultimately contributing to a more open and informed digital ecosystem that values personal freedom.
Understanding Diehdfpem and Its Role
The role of Diehdfpem in the online ecosystem warrants careful examination, particularly in the context of activity documentation and user interaction tracking.
Diehdfpem functions as a vital component, enabling seamless data management and user engagement analysis. Its emphasis on Diehdfpem security ensures that user data remains protected, fostering a trustworthy environment that supports individual freedom while maintaining the integrity of online interactions.
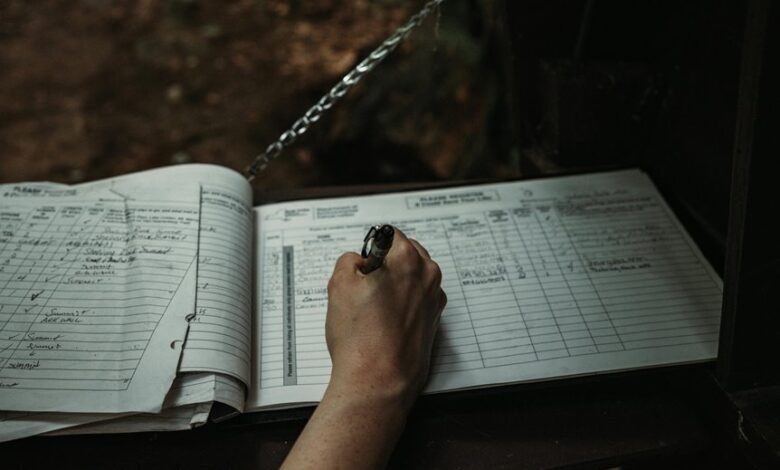
Best Practices for Managing Alerts Logs
Effective management of alerts logs is crucial for maintaining an organized and responsive online environment.
Implementing alert prioritization strategies ensures critical issues are addressed promptly, reducing potential risks.
Additionally, establishing clear log retention policies safeguards essential data while optimizing storage resources.
Tools and Strategies for Enhanced Security
Enhancing security in online environments requires a multifaceted approach that integrates various tools and strategies.
Effective security tools, such as firewalls and intrusion detection systems, must be employed alongside rigorous threat assessment protocols.
Conclusion
In conclusion, diligent documentation of online activities, particularly concerning Diehdfpem and alerts logs, is crucial for maintaining a secure digital environment. Research indicates that organizations employing robust log management practices can reduce security incident response times by up to 90%. This statistic underscores the significant impact of effective log management on operational efficiency and user trust. Ultimately, prioritizing these practices not only enhances security but also fosters a more informed and engaged user base.